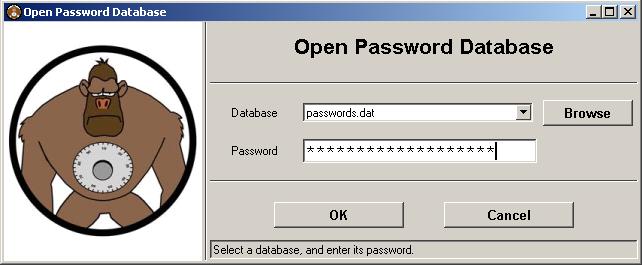
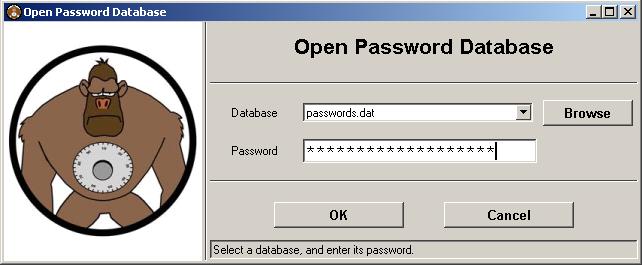
Upon start-up, Password Gorilla shows the "Open Password Database" dialog. It shows a list of recently used password database files, allows you to browse for a different password database file, and asks for the database's master password. Once a file is chosen, and the master password is entered correctly, the password database is opened, and its contents are shown.
To create a new, empty password database, click the "Cancel" button, and then select "New" from the "File" menu. You will be asked for an initial master password for the new password database.
It goes without saying that the master password should be non-trivial. I.e., the master password should not be a word in any language nor a name. Such trivial passwords are subject to dictionary attacks, in which an attacker could gain access to your master password by simply using "brute force," by trying all the words in the dictionary.
Equally important is that the master password should not be kept in the same place as the password database. Ideally, the master password should not be written down at all, so that it remains in your personal memory only. If you decide to write down your master password, keep it away from your computer(s), in a location that only you know of.
Because the password database is encrypted using your master password (using the peer-reviewed and commercially well-accpted Twofish algorithm, for the technically inclined), it is imperative that you do not forget your master password. It is impossible to recover a lost master password. An encrypted password database can not be "cracked," as long as the master password is not trivial (see above).
Note that Password Gorilla does not try to second-guess your choice of password. It does not check for or complain about passwords that would generally be considered weak.
Logins in the password database are shown as a tree, organized into nested groups. Groups allow you to arrange logins by category. Click on the plus sign next to a group's name in order to view its subgroups and logins that the group contains.
New groups and subgroups can be added by right-clicking on a group name, and choosing the "Add Subgroup" option. (Macintosh users, hold the Control key, and click on a group name.) In the dialog box that opens, the "Parent Group" name will be set automatically, and the name of the new subgroup can be entered.
You can also drag both groups and logins, and drop them on a new parent group, to quickly re-arrange the database's organization.
Note that empty groups are not stored in the password database file. If you save and re-open a file, empty groups will disappear.
Groups can contain any number of logins. To add a new login, right-click on a group, and choose the "Add Login" option. To edit an existing login, right-click on an login, and select the "Edit Login" option. (Macintosh users, hold down the Control key, and click on a group name.)
The following information is managed for each login:
When editing a login, the password is not shown, for added protection from curious onlookers. You can click the "Show Password" button to toggle visibility of the password.
Clicking on "Generate Password" generates a new pseudo-random password according to the current password policy (which is a per-database setting that can be set using the "Password Policy" option in the "Manage" menu). If the "Override Password Policy" box is checked, you can edit the password policy to use for this one password.
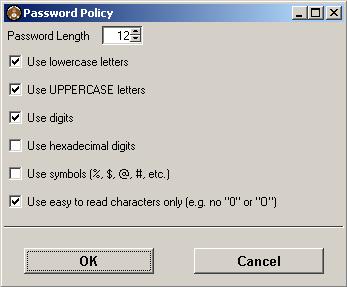
The password policy allows you to set the length of randomly generated passwords, and the characters to use. Check the "use easy to read characters only" option to avoid characters that look similar. This excludes the lower- and uppercase letters 'i', 'j', 'l' and 'o', the digits '0' and '1', and the exclamation mark, pipe symbol, and parentheses. Note: to generate random hexadecimal passwords, the "use hexadecimal digits" option should be checked exclusively, and the password length should be an even number.
The default password policy for the current database can be set using the "Password Policy" dialog from the "Manage" menu.
General, database default and export preferences can be configured using the "Preferences" dialog from the "File" menu. Database preferences, which are specific to the current password database, can be configured using "Database Preferences" from the "Manage" menu, when a database is open.
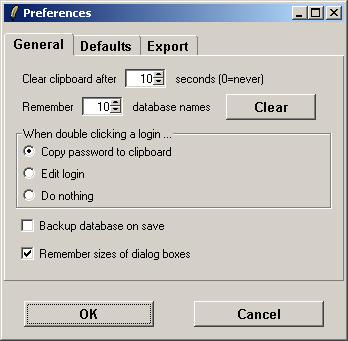
.bak" extension.
Database default preferences are applied to new databases, but do not affect existing databases. To change a setting for an existing database, go to "Database Preferences" in the "Manage" menu. See the discussion of Database Preferences below.
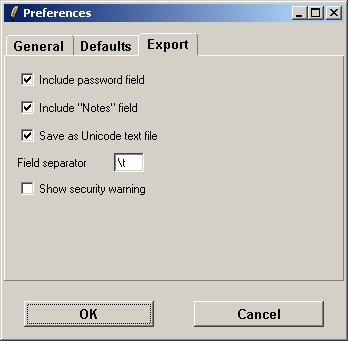
Export preferences apply to the exporting of a password database to a plain-text file.
These database preferences can be configured using "Database Preferences" from the "Manage" menu.
It is highly recommended to enable this option, and to upgrade existing databases to the Password Safe 3 format, which features enhanced security. See below, Information about the new Database Format, for more information.
Note that this option can only be changed on a per-database basis and does not appear in the Database Default Preferences Menu. This prevents a malicious user from changing the preference in the registry and degrading the protection of future databases.
It is recommended to use the new format, and to upgrade existing password databases, unless you require compatibility with software that supports the old format only, such as Password Safe 2.x, or versions of Password Gorilla prior to 1.4.
Password Safe recommends to use the ".psafe3" extension for V3-format database files, and the ".dat" extension for V2-format files. (Password Gorilla allows password database files in either format to have any extension.)
Just like re-using the same passwords over and over again, or keeping passwords written down on a sticker glued to the bottom of your desk, some risks are associated with the use of Password Gorilla. This section is not meant to scare you, but as an educated user, you have the right to know about potential risks, and to make informed decisions. Risks should not be ignored, but evaluated and addressed.
There are different threat vectors that can be considered:
First of all, the software itself may be a risk. For all you know, the software's author could be a sociopath who tries to talk you into downloading and installing buggy software that secretly broadcasts your passwords. If you want, you can trust the author, third-party recommendations, you can inspect the source code for trap doors, or trust a third-party code inspection.
Maybe the software is not bug-free. In an extreme scenario, a bug in Password Gorilla could destroy your password database. It is good advice to keep a backup copy of your password database in a safe place.
Sometimes, computers have the annoying habit to crash at the most unfortunate time. Many users have lost data due to an unpredicted crash. This can be problematic, e.g., when you just added or modified a login, and did not get around to saving the updated password database. If a password was randomly generated, it may be lost.
The easy workaround is to not confirm your password with the online service before saving the password database. I.e., when creating a new login, first add it in Password Gorilla, and immediately save the database (using "Save" from the "File" menu). Only then go to your online service -- e.g., the Web site that required registration, and complete its signup process. When modifying a login, e.g., changing the password, there is a chance that the computer might crash after saving the database, but before completing the service's password change process. In this case, the old password will still be available in the password database's backup file -- assuming that you have a backup copy, of course.
Common sense will go a long way in protecting your password database from other users that you share a computer with. Never keep Password Gorilla running when you leave the desktop unlocked. Make sure that the database file is not readable by other users -- while the database format is considered secure, this prevents other users from copying the file, and making a brute-force attempt of guessing the master password offline.
If you follow these precautions, there is nothing to worry about here.
If your computer is administered by somebody else than you, then you need to trust the administrator(s). An administrator can bypass the operating system's security measures, and inspect a running program's in-memory data. Password Gorilla obviously needs to have the decrypted contents of your password database in memory, so a malicious administrator could access Password Gorilla's memory, and gain access to your passwords. In an attempt to foil naive attackers, Password Gorilla takes some care by not storing data in clear text, but encrypted using a temporary key. However, because the key is also kept in memory by necessity, a motivated attacker could find both the encrypted password and its key.
Of course, malicious administrators have a wide range of tools at their disposal that invade on your privacy, in order to gain access to your passwords. An administrator could replace the Password Gorilla software with a trojan version that looks and acts the same, but sends your passwords to the administrator's account. Even if you are not using Password Gorilla, the administrator could install a key logger, or monitor your internet connection, to find passwords as you type them.
The added risk of using Password Gorilla is that a malicious administrator could compromise all passwords at once, instead of only intercepting the few passwords that you actually use and transmit in one session.
If your computer is infected by spyware or viruses, then external malicious users may have control over your computer. Such users could use the same attacks as described for a system administrator above. It is a good idea to check for viruses and spyware on a regular basis. Password Gorilla should obviously not be used on a compromised computer.
The above does not necessarily imply that Password Gorilla is too unsecure to use. They are merely a set of risks that need to be considered and evaluated in order to make an informed decision, and to take some common sense precautions. The author believes that using Password Gorilla is a better idea than the alternative of writing down passwords, or of reusing passwords.
As the example of the malicious system administrator shows, there is a wide range of attacks that are possible even if you were not using Password Gorilla.
Saying that Password Gorilla should not be used on a computer that is infected with spyware, viruses, or backdoors, is good advice, but redundant, as the problem is not limited to Password Gorilla. A compromised computer should not be used for anything, especially not for private communication.
Also, while technical attacks receive a lot of publicity, it should not be forgotten that social engineering attacks are usually more effective. In a study that I read about, a sizeable fraction of users revealed their passwords to strangers on the street, for a mere piece of chocolate. In one of the Hollywood movies that treat this subject better than others, War Games, the protagonist gains access not by pressing a magic button, or by bypassing security, but by spending countless hours trying to get into the designer's mind, in a social engineering attack to guess the designer's most likely choice of password -- another reason to prefer random passwords.

Frank Pilhofer, fp -AT- fpx.de